THE WORLD OF WIFI, DAS, AND PRIVATE CELLULAR
It’s no longer just Indoor Connectivity! Modern environments span buildings, campuses, outdoor yards, and loading docks, all with users, devices, and IoT endpoints that need to move freely across the network without dropping a connection.
- Buildings: Offices, warehouses, healthcare facilities
- Campuses: Multi-building environments and open grounds
- Devices: Laptops, phones, forklifts, carts, sensors
- IoT: “Always-on” endpoints intolerable to gaps or outages
What customers are asking for has evolved well beyond basic coverage. The general expectation today is a network that performs under load, follows users and devices across all spaces, and gives IT the ability to control and enforce policy at every layer and corner.
What customers expect
Performance: Consistent, low-latency throughput regardless of location, device count, or application type.
Mobility: Devices move. The network must move with them seamlessly and without re-authentication or dropped sessions or connectivity.
Security and Control: Identity-based access, segmentation, and policy enforcement that IT can see and manage.
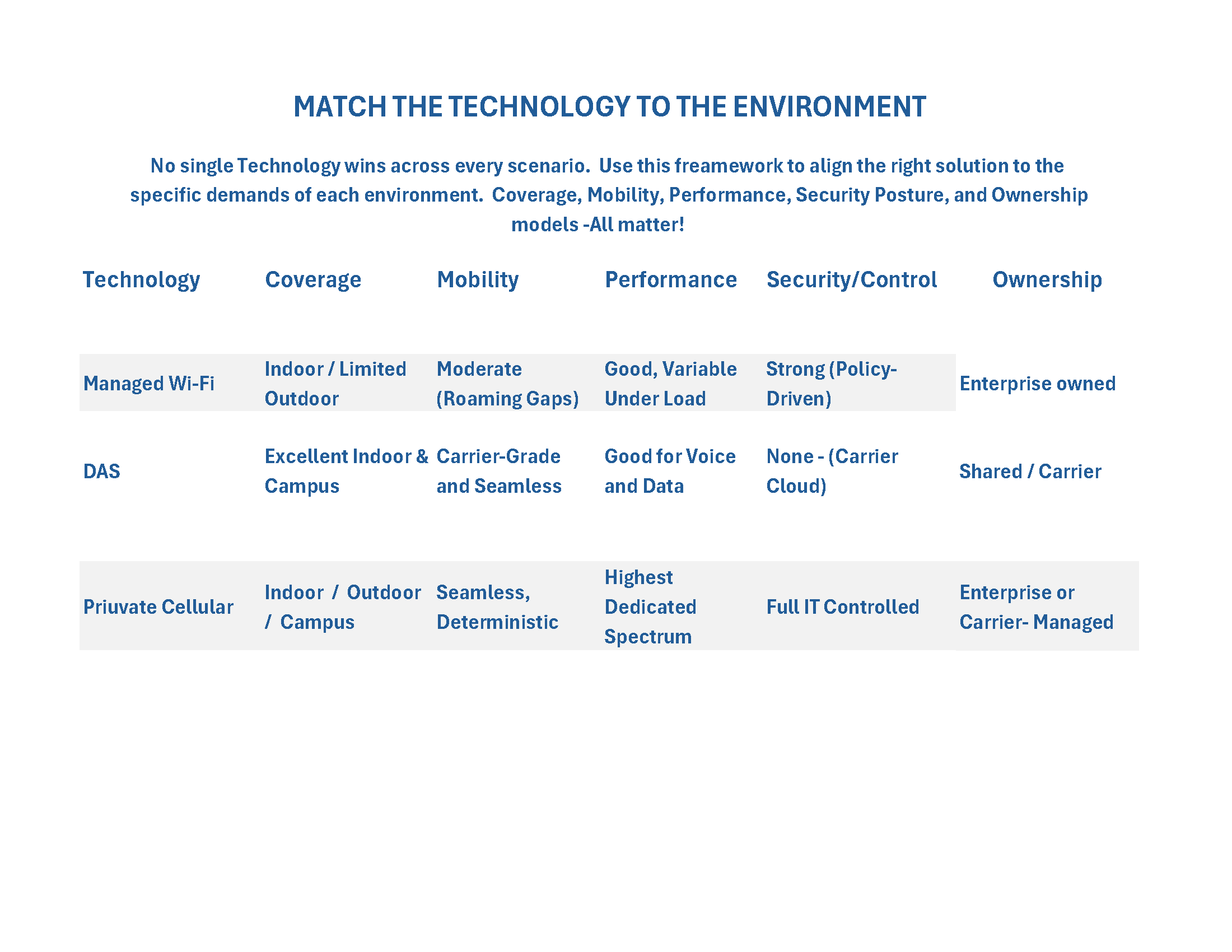
What Works in One Space, Fails in Another
No single technology solves every environment. Each deployment scenario reveals different failure events. The wrong choices leave real gaps in coverage, continuity, and control.
- Coverage Gaps: Densely structured buildings with thick walls and outdoor environments create “dead zones” that typical Wi‑Fi access points cannot reach with consistency and reliability.
- Mobility Disruption: Devices roaming between access points or moving across building boundaries lose sessions, re-authenticate, or drop connections at the worst moments.
- Security Limitations: Shared mediums, open SSIDs, and lack of device-level visibility expose the network to lateral movement and unauthorized access.
Most Conversations Start with Wi‑Fi
Wi‑Fi is the default and for good reason. It’s familiar, widely deployed, cost effective to install, and sufficient for the majority of indoor office and campus environments. It’s the starting point for almost every connectivity conversation.
Public WI‑FI vs. Managed WI‑FI
Not all WI‑FI is equal. The difference between an open hotspot and a properly managed enterprise network is enormous in security posture, operational visibility, and what IT can actually control.
- Open SSID: No authentication
- Shared medium with unknown users
- No segmentation or policy enforcement
- No visibility into connected devices
- Identity-based access control
- Network segregation by role or device
- Policy-driven traffic management
- Full visibility and login requirements
- Designed for enterprise environments
Flexible, Scalable, and Segmented: Managed Wi‑Fi gives IT teams the tools to run multiple logical networks over shared infrastructure, separating employees from guests, segmenting IoT devices, and enforcing granular policies without additional hardware.
- Employee Networks: Full access, identity-authenticated, policy enforced
- Guest Networks: Isolated, bandwidth-limited, no internal/private access
- IoT / Device Segmented: Dedicated VLAN, restricted lateral movement
As a Shared Medium — Inconsistent Outcomes
Wi‑Fi is a shared radio medium. When interference increases, devices roam, or users move outdoors, performance becomes unpredictable, and for mission-critical applications, unpredictability is not acceptable.
- RF Interference: Neighboring networks, Bluetooth, dense device populations, and physical obstructions diminish availability.
- Roaming Gaps: Handoffs between access points are not always seamless — especially for latency-sensitive voice, video, or real-time applications.
- Distances Outdoors: Wi‑Fi range and reliability drop significantly in open outdoor environments without careful AP placement and density.
When a DAS (Distributed Antenna System) is Needed
Thick wall buildings, underground spaces, lengthy warehouse structures, or greater distances from cell towers may reduce or inhibit cellular coverage or signal penetration. A DAS re-broadcasts the carrier signal throughout a building or campus by distributing small antennas connected to a central signal source. It solves the carrier coverage problem without requiring users to change behavior or connect to a different network.
Signal Flow: SIGNAL SOURCE >> HEAD-IN UNIT >> REMOTE AMPLIFIERS >> REMOTE ANTENNAS
Traditional DAS vs. Targeted Solutions
- Traditional DAS: Designed for stadiums, airports, large venues; custom engineered; multi-carrier capable; high cost and long construction times; requires carrier coordination.
- Cel-Fi and Targeted Solutions: Purpose-built for enterprise buildings; pre-engineered for faster deployment; lower cost and simpler installation; ideal for mid-sized facilities; carrier-accepted signal boosting.
Mobility and Control
Coverage alone is not the answer when devices do not stay still. For instance, forklifts crossing a yard or entering a different room, healthcare carts moving between floors, or field workers covering large outdoor areas. The network needs to maintain the session, enforce policy, and keep performance stable throughout the journey.
- Logistics and Warehousing: Forklifts, scanners, and WMS terminals moving across large floorplans.
- Healthcare: Clinical carts, patient monitoring, and staff devices roaming across multiple floors and facilities.
- Outdoor Operations: Field workers, vehicles, and remote sensors across yards, lots, and open campuses.
Private Cellular — A different Model
Private LTE and 5G networks operate on licensed or CBRS spectrum and are fully owned and controlled by the enterprise. Unlike carrier cellular or Wi‑Fi, private cellular is purpose-built for deterministic performance, seamless mobility, and IT-managed access.
- Deployed on a dedicated spectrum: CBRS licensed LTE/5G or shared spectrum isolated from public networks
- Managed access via SIM: Only devices with provisioned SIM cards can connect
- Integrates with enterprise systems: Firewalls, SD‑WAN, SIEM, identity control (SASE or ZTNA)
Built for Mobility, Performance and Security
Private cellular addresses Mobility, Performance, and Security simultaneously — deterministically rather than best-effort. This is the key differentiator from both Wi-Fi and carrier DAS.
- Mobility: Seamless Hand-offs across cells with no re-authentication necessary
- Performance: Dedicated spectrum means on contention with public users. Low latency and high reliability provides deterministic outcomes for mission critical Workloads
- Security and Control: SIM based authentication for IT visibility, policy enforcement, and segmentation. All within the enterprise perimeter.
In Conclusion
Such complicated decisions require expert analysis and guidance only available from the resources of capable and seasoned engineers and vendors. No matter how gifted an organization’s IT staff might be, these decisions require sophisticated tools and surveys. The conversation starts with a Trusted Advisor who can open the journey of discovery by asking the right questions and having access to the appropriate engineers and vendors for each situation.
 SEDCOR
SEDCOR