Secure Access Built for the Modern Enterprise
The modern workforce is no longer confined to a corporate network perimeter. Users work from home, branch offices, airports, and cloud platforms—while applications live across data centers, SaaS platforms, and public clouds. Traditional Virtual Private Networks (VPNs), designed decades ago, were not built for this reality.
Zero Trust Network Access (ZTNA) replaces the outdated “trust but verify” model with a “never trust, always verify” approach—dramatically reducing cyber risk while improving user experience.
What Is ZTNA?
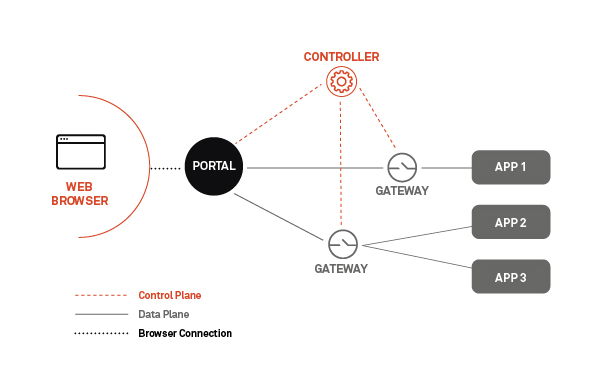
Zero Trust Network Access (ZTNA) is a security model that provides identity-based, application-level access to corporate resources—without placing users on the internal network.
Instead of granting broad network access, ZTNA:
- Verifies who the user is
- Confirms device posture and security status
- Evaluates context (location, behavior, risk signals)
- Grants access only to specific applications, not the entire network
Access is continuously evaluated—not just at login.

Why ZTNA Matters Today
Organizations face:
- Increased remote and hybrid work
- Rapid cloud and SaaS adoption
- Sophisticated ransomware and lateral-movement attacks
- VPN performance bottlenecks and security blind spots
ZTNA addresses all of these challenges by removing implicit trust from the network.
Key Benefits of ZTNA
🔐 Stronger Security
- No network exposure—applications are invisible to attackers
- Prevents lateral movement inside the environment
- Reduces attack surface dramatically
- Enforces least-privileged access by default
👤 Identity-First Access
- Access tied to user identity, not network location
- Integrates with MFA, SSO, and identity providers
- Continuously validates users and devices
☁️ Cloud-Ready by Design
- Ideal for SaaS, IaaS, and hybrid environments
- Eliminates backhauling traffic through data centers
- Works seamlessly across multi-cloud architectures
⚡ Better User Experience
- Faster access to applications
- No full-tunnel VPN connections
- Automatic, seamless authentication
📉 Reduced Operational Complexity
- Less VPN infrastructure to manage
- Simplified policy enforcement
- Easier onboarding/offboarding of users and vendors
ZTNA vs. Traditional VPN
A Side-by-Side Comparison
| Feature | ZTNA | Traditional VPN |
|---|---|---|
| Trust Model | Zero Trust (never implicit) | Implicit trust once connected |
| Access Scope | Application-specific | Full network access |
| Attack Surface | Minimal | Broad |
| Lateral Movement Risk | Very low | High |
| Cloud Optimization | Native | Poor |
| Performance | Direct-to-app | Backhauled traffic |
| User Experience | Seamless | Often slow & complex |
| Scalability | High | Limited |
| Third-Party Access | Granular & controlled | Risky |
Why VPNs Are No Longer Enough
VPNs were designed when:
- Users worked inside offices
- Applications lived in one data center
- Threats were less sophisticated
Today, VPNs:
- Create a single point of failure
- Grant excessive access
- Struggle with scale and performance
- Increase ransomware blast radius
ZTNA modernizes secure access by removing the network from the equation entirely.
Who Should Use ZTNA?
ZTNA is ideal for:
- Remote and hybrid workforces
- Cloud-first and SaaS-heavy organizations
- Companies with compliance requirements
- Businesses seeking to reduce ransomware risk
- Enterprises modernizing legacy security architectures
The Business Impact
By adopting ZTNA, organizations typically achieve:
- Reduced breach risk and dwell time
- Improved productivity and user satisfaction
- Lower infrastructure and operational costs
- Stronger compliance and audit readiness
- Future-proof security architecture
The Bottom Line
ZTNA is not just a VPN replacement—it is a security transformation.
As networks dissolve and identities become the new perimeter, ZTNA provides the visibility, control, and protection required for today’s distributed enterprise.
Secure users. Protect applications. Eliminate trust.

 SEDCOR
SEDCOR